Secure and Reliable Information Management Through Cloud Provider
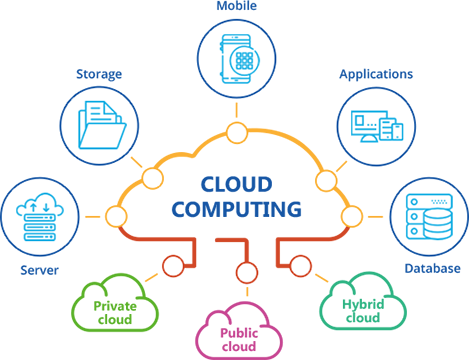
In the ever-evolving landscape of data administration, the utilization of cloud solutions has become an essential remedy for organizations seeking to strengthen their data safety actions while simplifying functional performances. universal cloud Service. The complex interaction between guarding sensitive details and making certain smooth ease of access poses a facility difficulty that organizations have to navigate with persistance. By checking out the subtleties of secure data administration with cloud solutions, a deeper understanding of the modern technologies and techniques underpinning this paradigm shift can be unveiled, clarifying the multifaceted benefits and considerations that shape the contemporary data administration environment
Relevance of Cloud Services for Information Management
Cloud solutions play an important duty in modern-day information management methods due to their cost-effectiveness, scalability, and access. Additionally, cloud solutions give high accessibility, making it possible for individuals to accessibility information from anywhere with a web connection.
Furthermore, cloud solutions supply cost-effectiveness by eliminating the demand for purchasing costly equipment and maintenance. Organizations can choose subscription-based versions that align with their budget plan and pay just for the sources they use. This helps in reducing upfront costs and overall functional expenditures, making cloud services a sensible alternative for services of all dimensions. In essence, the relevance of cloud services in information monitoring can not be overstated, as they provide the essential tools to simplify operations, improve cooperation, and drive business development.
Key Protection Difficulties in Cloud Information Storage

To attend to these security obstacles, organizations require durable safety procedures, including encryption, access controls, normal safety audits, and staff training. Partnering with relied on cloud provider that provide sophisticated security functions and conformity accreditations can likewise assist minimize risks connected with cloud information storage. Eventually, a proactive and extensive technique to safety is critical in guarding information kept in the cloud.
Implementing Data File Encryption in Cloud Solutions
Carrying out data file encryption in cloud remedies involves using durable file encryption algorithms and safe and secure crucial management practices. File encryption secrets need to be kept separately from the encrypted information to add an added layer of defense. Additionally, companies have to consistently upgrade security keys and employ solid accessibility controls to restrict that can decrypt the data.
Moreover, data file encryption should be used not only during storage yet also throughout data transmission to find out this here and from the cloud. Protected communication procedures like SSL/TLS can aid guard information en route, making certain end-to-end encryption. By prioritizing data security in cloud solutions, organizations can reinforce their information protection posture and keep the confidentiality and honesty of their delicate info.
Best Practices for Data Backup and Healing

Additionally, carrying out regular healing drills is necessary to evaluate the performance of back-up treatments and the company's capability to restore data swiftly. Automation of backup procedures can simplify operations and lower the possibility for human error. File encryption of backed-up data includes an additional layer of safety, protecting sensitive information from unapproved gain access to during storage space and transmission. By adhering to these finest practices, businesses can boost their data resilience and make sure seamless operations when faced with unanticipated occasions.
Monitoring and Auditing Information Accessibility in Cloud
To keep information integrity and safety within cloud atmospheres, it is essential for companies to develop durable actions for tracking and auditing data access. Auditing data gain access to goes a step additionally by providing a comprehensive document of all data gain access to activities. Cloud service providers frequently provide tools and solutions that assist in surveillance and bookkeeping of data access, enabling companies to gain understandings into just how their information is being utilized and guaranteeing liability.
Conclusion
In conclusion, cloud services play an essential role in making sure reliable and protected information monitoring for organizations. By resolving vital safety challenges with data encryption, backup, recovery, and monitoring practices, companies can safeguard sensitive information from unauthorized gain access to and information breaches. Carrying out these finest practices in cloud options advertises data integrity, discretion, and ease of access, ultimately enhancing partnership and efficiency within the company.
The crucial security challenges in cloud information storage revolve around data breaches, data loss, conformity laws, and information residency concerns. next page By securing information before it is uploaded to the cloud, organizations can minimize the danger of unauthorized accessibility and data breaches. By prioritizing information security in cloud solutions, companies can bolster their information safety position and maintain the discretion and stability of their sensitive information.
To maintain information honesty and security within cloud settings, it is vital for organizations to establish durable measures for tracking and bookkeeping information access. Cloud service suppliers typically offer devices and services that help with tracking and bookkeeping of information accessibility, enabling companies to get understandings into how their data is being made use of and ensuring accountability.